Apiiro Extends Container Security Platform to Runtime Environments
Apiiro has extended the reach of its cloud-native application security platform to enable it to analyze data from runtime environments. That capability provides developers with more context when it comes to remediating vulnerabilities before applications are deployed in a production environment.
Company CEO Idan Plotnik says the Apiiro platform extension will enable developers of container-based applications to understand how risks that are inherent to a runtime impact the security of the source code they are developing.
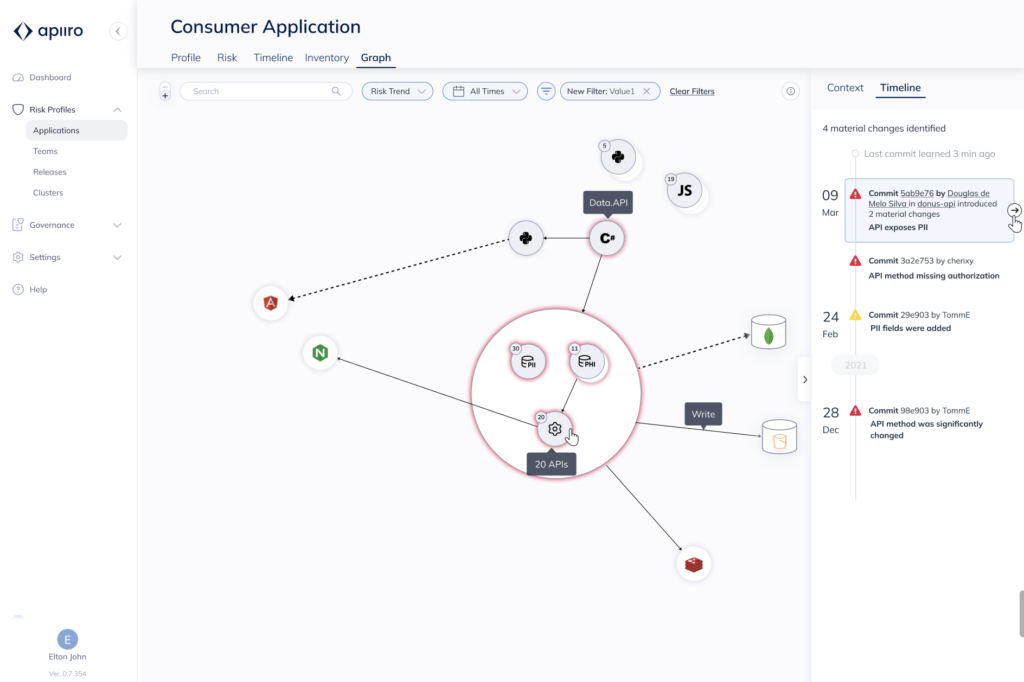
The Apiiro platform employs tools for scanning code for vulnerabilities that are integrated with graph technology that makes it possible to visualize all the dependencies that make up an application architecture, says Plotnik. That approach makes it possible to correlate risk to a specific container image that has been deployed on a runtime environment, he adds.
The overall goal is to make it feasible to shift responsibility for application security as far left as possible toward developers rather than trying to address security issues after a build has been integrated into a DevOps pipeline, notes Plotnik.
The Apiiro platform itself is based on a microservices architecture that was constructed using containers. However, it can also be employed to discover vulnerabilities in both cloud-native applications and legacy monolithic applications, says Plotnik. However, the bulk of adoption thus far has been in container environments where dependencies between microservices make cybersecurity especially challenging, he adds.
Once a vulnerability is discovered, Apiiro can automatically remediate issues involving a third-party open source component or platforms that have been programmatically configured using infrastructure-as-code (IaC) tools. As far as code that developers themselves created, Plotnik says Apiiro will surface remediation recommendations. However, it will be up to the individual developers to decide whether or not to implement those recommendations.
It’s not clear just how far application security can be shifted left. Each individual developer has differing levels of cybersecurity skills. However, as more security tools are provided to developers, the total number of vulnerabilities making it into production environments should significantly decline. That should ultimately improve organizations’ cybersecurity posture because the majority of breaches can be traced back to a known vulnerability issue, Plotnik adds.
The issue that developers of microservices-based applications encounter is that these environments are much more dynamic than legacy monolithic applications. Developers are constantly ripping and replacing containers to either add new functionality or fix an issue that has arisen. The challenge is that it’s not easy to perform vulnerability scanning on all the code encapsulated within a container.
Of course, many developers are hoping that containers with known vulnerabilities and misconfigurations will be replaced before cybercriminals are able to discover them. However, many containers are now running for longer periods of time as more stateful applications are built using containers deployed on Kubernetes clusters. The longer a container runs, the more likely it is a cybercriminal will find a way to exploit vulnerabilities.
One way or another, increased focus on securing software supply chains and the adoption of DevSecOps best practices will eventually improve overall application security. The challenge is getting the right tools in the hands of developers to achieve that goal sooner rather than later.