SafeBreach Adds Docker Support to Breach Simulation Platform
SafeBreach, a provider of a cybersecurity breach and attack simulation platform, today announced it has added support for applications built using Docker containers.
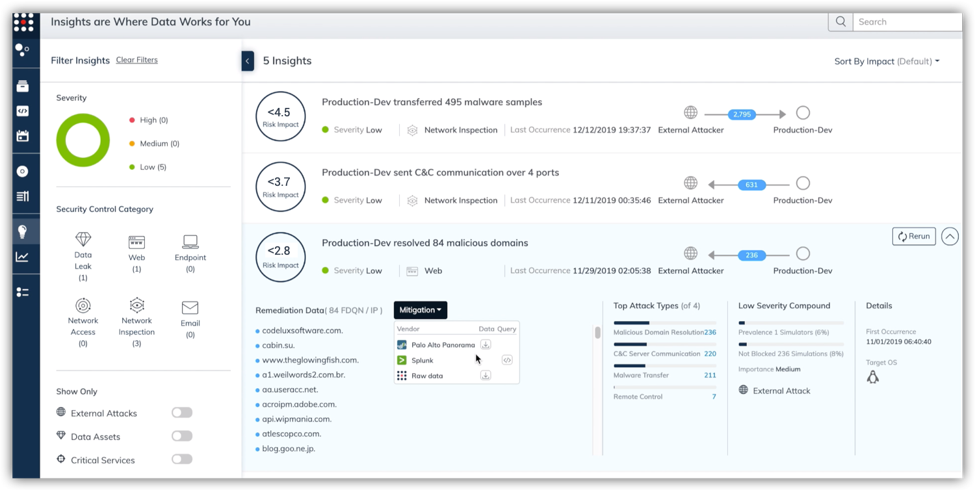
At the same time, SafeBreach has added a risk-based vulnerability management module through which the company will clearly rate vulnerabilities based on the results of attack simulations launched against both hosts and networks.
In the case of Docker containers, SafeBreach simulates attacks against the Docker data plane, network and API, including attacks that involve process injection, rogue applications, system changes and lateral movement from container to container. The Docker-based attack techniques are drawn from the “SafeBreach Hacker’s Playbook,” a collection of breach methods the company makes available to educate cybersecurity teams.
Yotam Ben Ezra, vice president of product for SafeBreach, said as organizations start to build and deploy applications based on microservices-based applications, many of them are wrestling with understanding how new vectors will be exploited by cybercriminals.
With this update, SafeBreach is making it possible to learn how various cyberattacks against containerized applications might unfold by running simulations of cyberattacks launched from various points of presence controlled by SafeBreach.
In general, Ben Ezra notes that most IT organizations have access to the tools and techniques required to thwart 99% of cyberattacks. The challenge they have is discovering what vulnerabilities might have been overlooked. Simulated attacks are a much more thorough approach to discovering known vulnerabilities than simply relying on a scan of a container, he notes.
Long term, it’s still not clear whether containerized applications will ultimately lead to more secure applications being built and deployed. On one hand, it’s easier to rip and replace containers than it is to patch an entire monolithic application. That capability should make it easier to remediate application vulnerabilities. On the other hand, microservices-based applications are more complicated, so securing the entire microservices ecosystem might prove to be more challenging, says Ben Ezra.
What’s more, developers are now building applications in a way that cybersecurity teams have neither visibility into nor control over, he adds. That situation is further aggravated as organizations take advantage of containers to deploy more applications on multiple cloud computing platforms, which, Ben Ezra notes, increases the size of the attack surface that needs to be defended.
Obviously, cybersecurity teams and developers of containerized applications will need to find a way to come to terms with one another as part of any effort to implement best DevSecOps processes. Developers may be assuming more responsibility for how controls are implemented. Cybersecurity teams, however, still define what controls are to be implemented and are then tasked with verifying they have been implemented. Yet, cybersecurity professionals don’t always trust developers to do the right cybersecurity thing when faced with pressing application delivery deadlines. The good news is that as developers are held more accountable for the application after it’s deployed in a production environment, many more of them have a vested interest in making sure their applications are secure.