CNCF Graduates Harbor Container Registry
The Cloud Native Computing Foundation (CNCF) announced today that the open source Harbor container registry has officially graduated, joining other projects such as Kubernetes and Prometheus monitoring software.
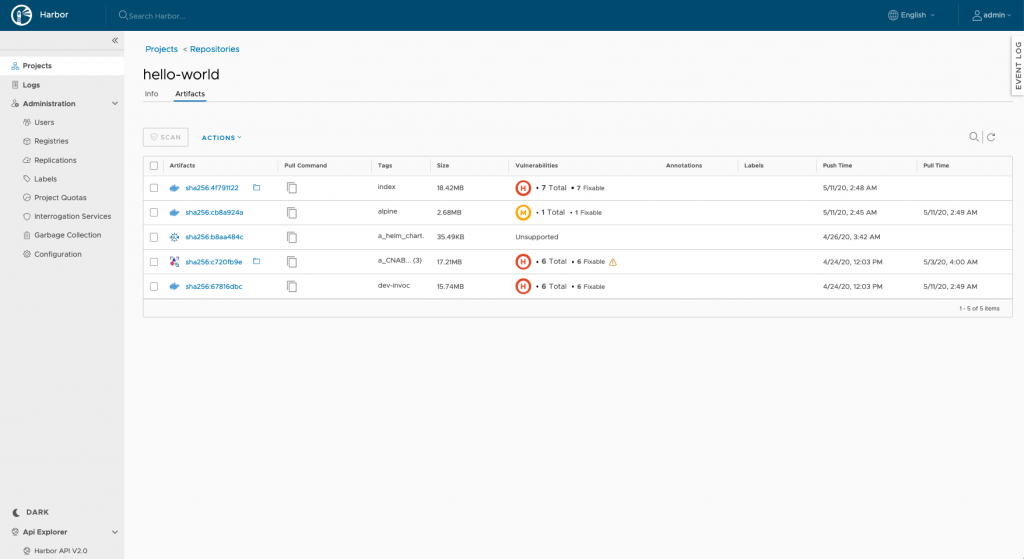
Originally developed by VMware, Harbor is an open source registry that secures artifacts by enabling IT teams to apply access controls to signed container images based on policies and roles. It also provides the hub that enables container security tools to scan for vulnerabilities more easily.
More than 83 organizations now contribute to Harbor, including Anchore, Aqua Security, Caicloud, DigitalOcean, Netease, Tencent, OVHcloud and VMware. There are now more than 300 community members.
Harbor became a CNCF project last summer, but VMware has been working on Harbor since 2014. Michael Michael, director of product management for VMware and a Harbor maintainer, says the fact that Harbor is more than 6 years old now helps account for why the project has been able to move comparatively quickly from incubation to graduation with the CNCF.
Going forward, Michael says he expects the community will focus on proxy caching to enable more peer-to-peer distribution of containers managed via Harbor. The rise of edge computing will require alternative approaches to pulling container images that are less centralized, he says.
The CNCF has also embraced Kraken, an open source registry based on a peer-to-peer architecture that was developed by Uber, and Dragonfly, a peer-to-peer based image and file distribution system.
Historically, organizations that have embraced containers have either built their own registry or relied on platforms such as DockerHub. It’s not clear how many organizations might eventually migrate to an open source registry from CNCF, but Harbor will clearly benefit over time from contributions being made by multiple vendors.
The project just released an update that adds support for the Open Container Initiative (OCI) specification for Kubernetes clusters. It’s now also possible to add other artifacts to the Harbor repository, such as Helm Charts.
Harbor 2.0 also makes it possible to create an OCI Index, a higher-level manifest that provides a representation of a bundling of image manifests so users can pull an image without having to specify the operating system and platform. The client tool instead makes sure the correct version of an image is pulled.
Other capabilities include support for Trivy as its default container image scanner and the ability to configure SSL to encrypt core Harbor services. Webhooks can now also be individually triggered.
As a means to bring some order to container management, registries are often underappreciated. However, as the number of containers employed in enterprise IT environments increases exponentially, the crucial role registries play in lifecycle management has become more apparent to both developers and IT operations teams.
It may be a while before most IT teams fully operationalize the management of containers and Kubernetes clusters. Naturally, those efforts require more tools and platforms than just a container registry. However, for organizations that are just getting started down that path, a container registry might be the best place to focus their initial efforts.