Isovalent Update Advances Cilium Networking
Isovalent has delivered an update to the open source Cilium network overlay for Kubernetes environments that adds support for the Gateway application programming interface (API) for Kubernetes along with integration with the open source Grafana visualization software. The update will improve overall observability using Grafana Tempo tracing data enriched with Hubble Layer 7 HTTP metrics.
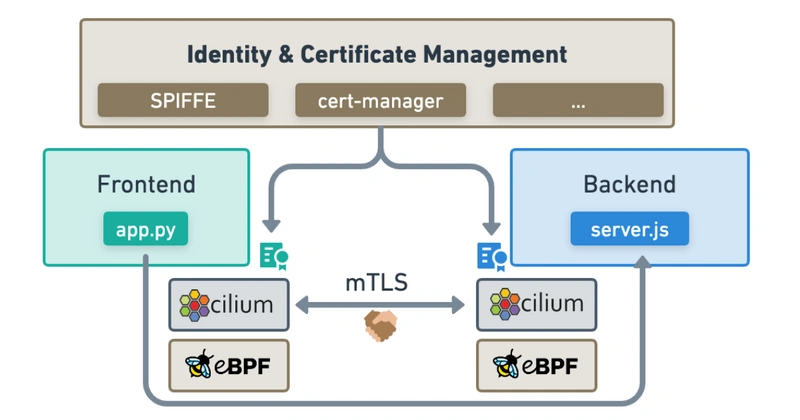
In addition, NetworkPolicy now matches Transport Layer Security (TLS) server name indication (SNI) names and the mTLS datapath has been merged with Cilium to create a foundation for a forthcoming proxy-free mTLS implementation to improve identity and certificate management within the context of a Cilium-based service mesh.
Support for BIG TCP, IP address management (IPAM) for LoadBalancer Kubernetes Services, stream control transmissions protocol (SCTP) support and additional NAT46/64 improvements have been added. Each Cilium image will now be signed in a way that creates a software bill of materials (SBOM) to also improve security.
Finally, there is a preview into the upcoming replacement for veth virtual Ethernet devices that will make container networking as fast as host networking.
Isovalent CTO Thomas Graf said version 1.13 of Cilium is the biggest update yet to a project that takes advantage of the extended Berkeley Packet Filter (eBPF) microkernel within Linux to enable fine-grained microsegmentation and accelerate networking performance.
While the Gateway API represents how traffic will be managed going forward in Kubernetes environments, Graf says the project will continue to support existing legacy approaches, such as per-request gRPC balancing using plain Kubernetes services with a couple of annotations that have now been added.
Overall, Graf says, the goal is to make networking in Kubernetes environments more accessible. The fact that NetworkPolicy can now match TLS SNI server names, for example, makes it simpler for the average IT administrator to implement a protocol for encrypting network traffic that today requires higher levels of programming expertise.
Those types of enhancements then make it simpler for a platform engineering team to centrally manage networking services across a fleet of Kubernetes clusters, he added. The next major goal is to then extend the reach of Cilium into legacy virtual machine environments using a “box” implementation of Cilium that runs on a virtual machine.
Adoption of eBPF is now being advanced by The eBPF Foundation, an arm of The Linux Foundation committed to enabling other platforms beyond Cilium to run as sandbox programs at the kernel level in any operating system. It may be a few more years before that vision is completely realized, but in the meantime, the number of networking, security and storage platforms that will take advantage of eBPF in the months ahead is expected to expand considerably.
In the meantime, networking across multiple Kubernetes clusters is becoming a more pressing issue as more cloud-native applications are deployed in production environments. A network overlay that connects application workloads across those clusters is needed to provide the foundation upon which microservices running on different clusters are integrated. The challenge, of course, is finding a way to deliver those networking services at a high enough level of abstraction that mere IT mortals can manage them alongside software engineers that have a lot more programming expertise.