Red Hat Acquires StackRox to Strengthen Container Security
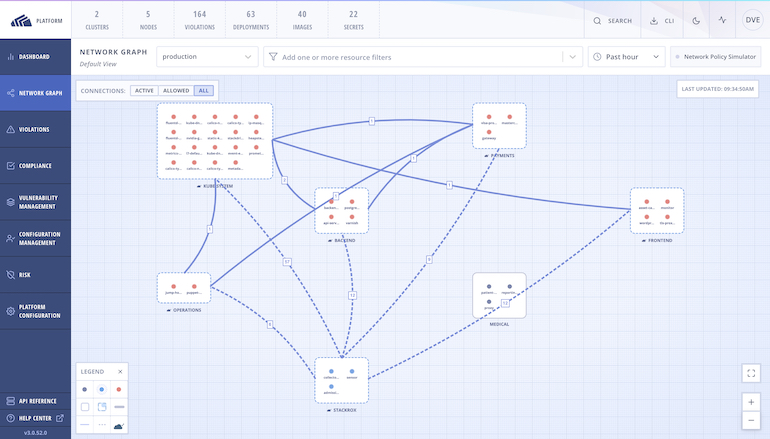
Red Hat this week announced it is acquiring StackRox, which provides a suite of tools for securing Kubernetes clusters.
Ashesh Badani, senior vice president for cloud platforms, says Red Hat will make the StackRox tools available as open source code, and will incorporate the container security expertise of StackRox’s team into the support services it provides.
Red Hat has an ongoing relationship with StackRox, specifically around Red Hat OpenShift, the application development and deployment platform based on Kubernetes, said Badani. StackRox’s approach to implementing security policies that run natively on a Kubernetes cluster has already been adopted by a number of Red Hat customers, notes Badani said.
The core StackRox policy engine includes hundreds of built-in controls to enforce security best practices, in addition to providing tools to address configuration management issues for containers and Kubernetes and the run time environments they are deployed on.
StackRox tools will continue to be available for other Kubernetes platforms, including Amazon Elastic Kubernetes Service (EKS), Microsoft Azure Kubernetes Service (AKS) and Google Kubernetes Engine (GKE) in addition to the Red Hat OpenShift platform.
The challenge for IT teams is securing increasingly complex, microservices-based software supply chains typically built using containers. Most organizations are still in the early stages of embracing DevSecOps best practices to achieve that goal. While there is no shortage of tools available for securing container platforms, the real challenge is putting the processes in place that enable DevOps and cybersecurity teams to easily collaborate.
StackRox CEO Kamal Shah says that collaboration, however, needs to happen in a way that doesn’t slow application development down. Otherwise, Shah said, the DevOps ‘body’ will reject the cybersecurity ‘organ.’
Of course, many developers assume containers are inherently more secure simply because they run for short periods and are quickly replaced. However, Shah notes, in most cases, developers are simply repeating and encapsulating the same vulnerable code, over and over, across IT environments running thousand of containers.
As the number of container applications deployed in production environments on Kubernetes clusters increases, container security will become a major concern. A recent survey published by the Cloud Native Computing Foundation (CNCF) finds 92% of respondents are now running containers in production environments, with 83% reporting they are also employing Kubernetes in those environments. But, as is often the case when it comes to emerging platforms in the enterprise, however, determining how best to secure those platforms largely remains an afterthought. Many developers continue to assume cybersecurity issues will be addressed by a separate cybersecurity team.
As such, it may take time before security fully shifts to the proverbial left. Nevertheless, as the tools required to secure these technologies become more widely available, achieving that goal is within sight.