KSOC Publishes SBOM Specification for Kubernetes
Kubernetes Security Operations Center (KSOC) this week published a Kubernetes Bill of Materials (KBOM) specification that promises to make it simpler to discover vulnerabilities.
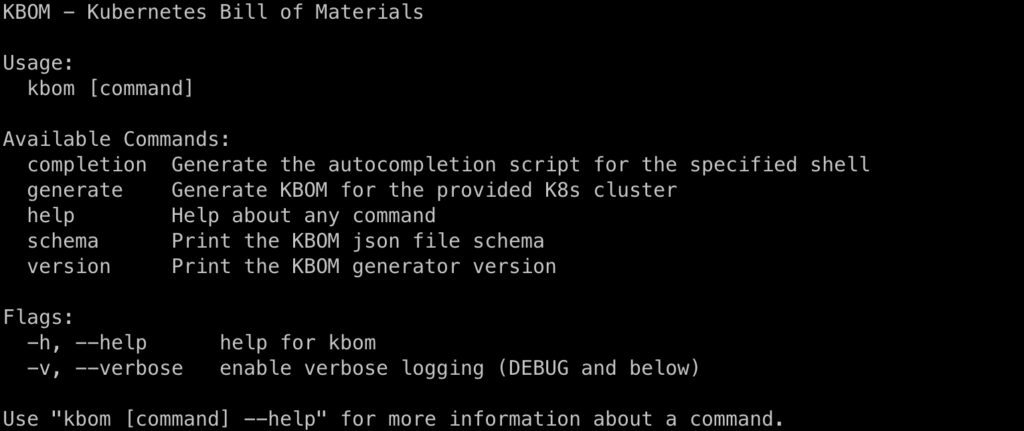
KBOM, available via an open source command line interface (CLI) tool, provides a quick view of workload count, cost and type of hosting service, vulnerabilities for both internal and hosted images, third-party customizations, authentication, service meshes and version details for the managed platform.
KSOC CTO Jimmy Mesta said the open source tool the company provides interrogates the Kubernetes application programming interface (API) to discover these components. That tool can be run as often as an IT team wants as frequent changes to the Kubernetes environment are made, he added.
While there is no shortage of tools for creating SBOMs, there are none specifically designed to work with the Kubernetes API, noted Mesta.
The specification should also make it simpler for IT teams to comply with various regulatory requirements, such as the SBOM mandate imposed on federal agencies by the Biden administration, he added.
The challenge that remains is that very few organizations have a process in place that enables them to operationalize SBOMs. In the months ahead, IT teams should expect to be held more accountable for the security of the software they employ as legislation is crafted to hold providers of applications more accountable for breaches.
Historically, organizations tended to allow developers to aggregate software components without always checking to see if they were compromised. Cybercriminals are becoming increasingly adept at injecting malware into software components in the hope that malware will find its way into any number of downstream applications. As such, IT teams are, at the very least, going to be required to attest that those components were scanned for vulnerabilities.
KSOC already provides a security posture management platform for Kubernetes that surfaces current and historical cyberattack activity and can generate an SBOM. In addition, the platform provides remediation guidance, scans for vulnerabilities, prevents workloads that don’t comply with defined policies from being deployed and aggregates what permissions have been granted to make managing role-based access controls (RBAC) simpler.
It’s apparent that cybersecurity is, once again, an afterthought as IT teams begin to adopt new cloud-native platforms for building and deploying applications. The issue now is finding a way to close that gap without requiring a lot of cybersecurity expertise to identify issues that can then be remediated by DevOps teams.
It’s not clear whether cybercriminals are specifically focusing on Kubernetes clusters, but as the routine scans they make start to surface more of them, it’s only a matter of time before they probe for weaknesses. Unfortunately, many of the Kubernetes clusters have been deployed by developers and DevOps teams with limited cybersecurity expertise so the probability that significant cybersecurity events involving Kubernetes clusters will be encountered is high. The challenge and the opportunity now is to apply an ounce of prevention today before a pound of cure is required tomorrow.